Andrew Bonwick
Vice President of Product Development at Relm Insurance
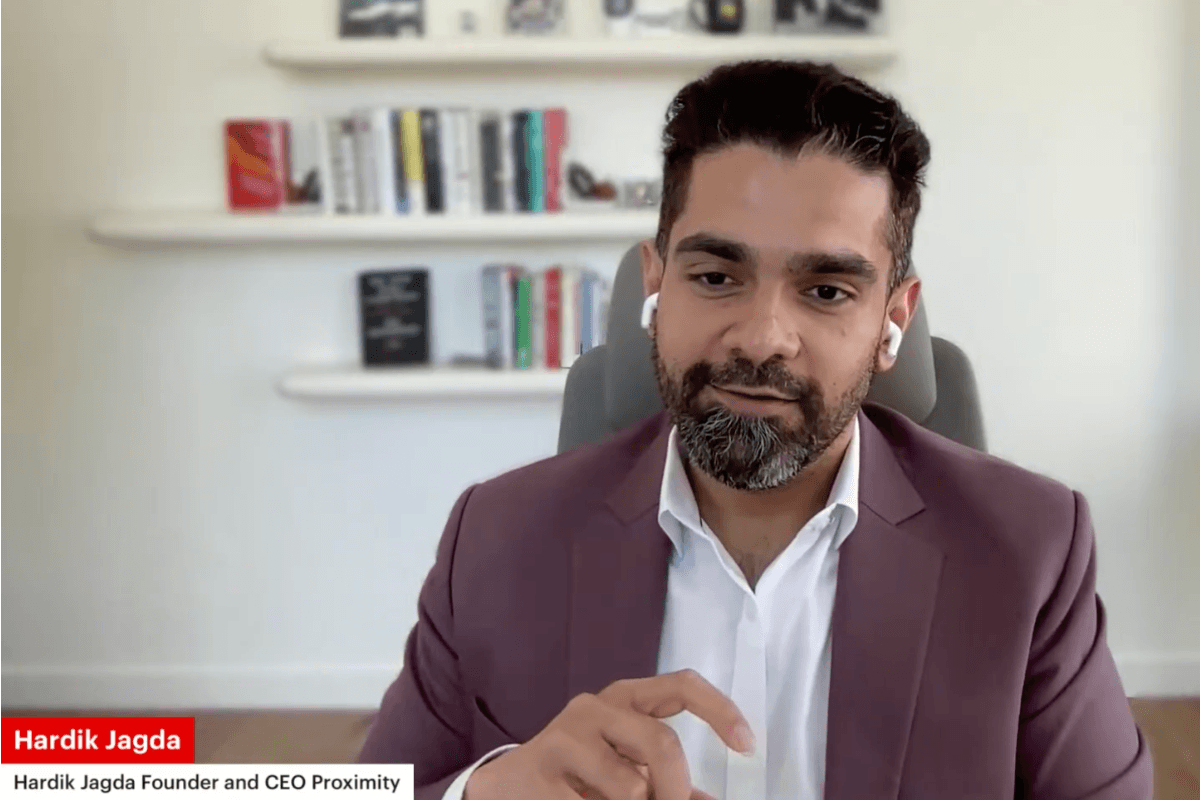
Madhav Sheth
CEO of Ai+ Smartphone
Varun Kashyap & Sridevi Reddy
Co-Founders, Zithara.ai
Transforming Indian Offline Retail and Customer Engagement Using AI
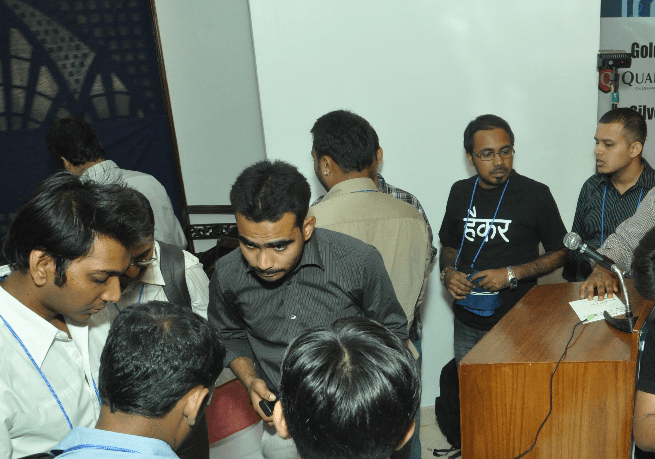
GSM networks has a critical security breach, as White hats demonstrated the the vulnerability of the widely accepted mobile technology at Nullcon, the International Security Conference 2012, held at Goa.
The white hats or the ethical hacker group Matrix Shell explained and showed the security holes of GSM technology deployed in India they also demonstrated a real hacking scenario using GSM network in real time.
The security experts of the team includes Akib Sayyed, Dipesh Goyel, Bipul Sahu and Nitin Agarwal. They said that anyone can impersonate another GSM mobile number by:
1. using IMSI and making calls
2. Possible threats include
3. identity theft
4. Huge mobile bills or no balance of the victims
5. An attacker can create a grid of such hardware and can empty the phone balance of each
subscriber in just less than 3 hrs.
6.The attacker can give misleading information by using some government employee’s identity or even use some law enforcement personsonal’s identity.
Chances of catching the attacker
There are very less chances to catch the attackers as he/she can change the imei,imeisv. The attacker can also spoof location by saying that his location is at 70 km away from the GSM base station even though he/she is sitting very near to the same GSM base station.
No encryption on Air Interface
Standard encryption on GSM should be a5/1 but in India the providers mostly use a5/0 I.e. no encryption. In this scenario the attacker can use some open source software to sniff the communication from air and can listen to the calls easily.
The reasons as we suspect why these GSM configuration issues exist in the telecom networks
It takes less time to setup session between mobile phone and BTS if no encryption is used also less load on the systems.