With ever growing identity theft incidents and economic frauds, mobile and internet users are required to be very vigilant about whatever they do. Whatever be our attempts to safeguard our data what can be done if someone responsible for safe handling of data is not caring enough? This exactly was the situation with Airtel customers for a good part of the time. While telcos like Airtel provide reasonably good online facilities, someone who thinks a little more would be able to harvest decent amount of data about their customers - the mobile handset make, number of recharges done etc.
Mobile Handset Details Revealed
If an user attempts to obtain mobile internet settings from Airtel website (link not attached on purpose), the confirmation screen displays the model of the handset. This is fine if you are doing this for your handset, it is certainly not OK if you are keying in some random phone number.
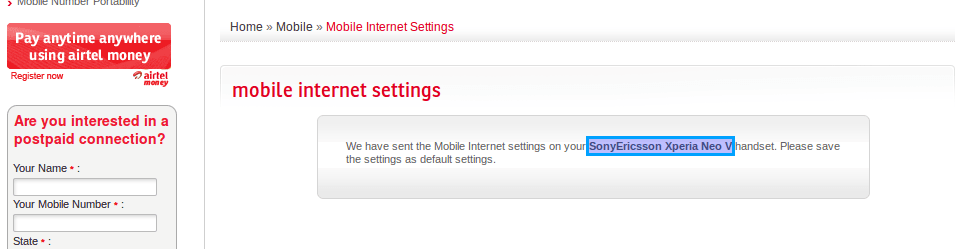
Trouble factor: Someone just needs to key in a phone number and the captcha code. This makes it possible:
For anyone to spam any Airtel number with innumerous settings messages at any time of the day.
The receiver would be clueless as to why settings are being pushed on a continuous basis and will be left thinking if Airtel has gone nuts :P
Airtel would not be in a position to find the originating computer easily. Even if they manage to trace the IP, rest of the process would be very lengthy and by then damage would be done
There is also a remote possibility of hi-tech mobile thieves using this method to identify their prey once they get a list of mobile numbers in their area.
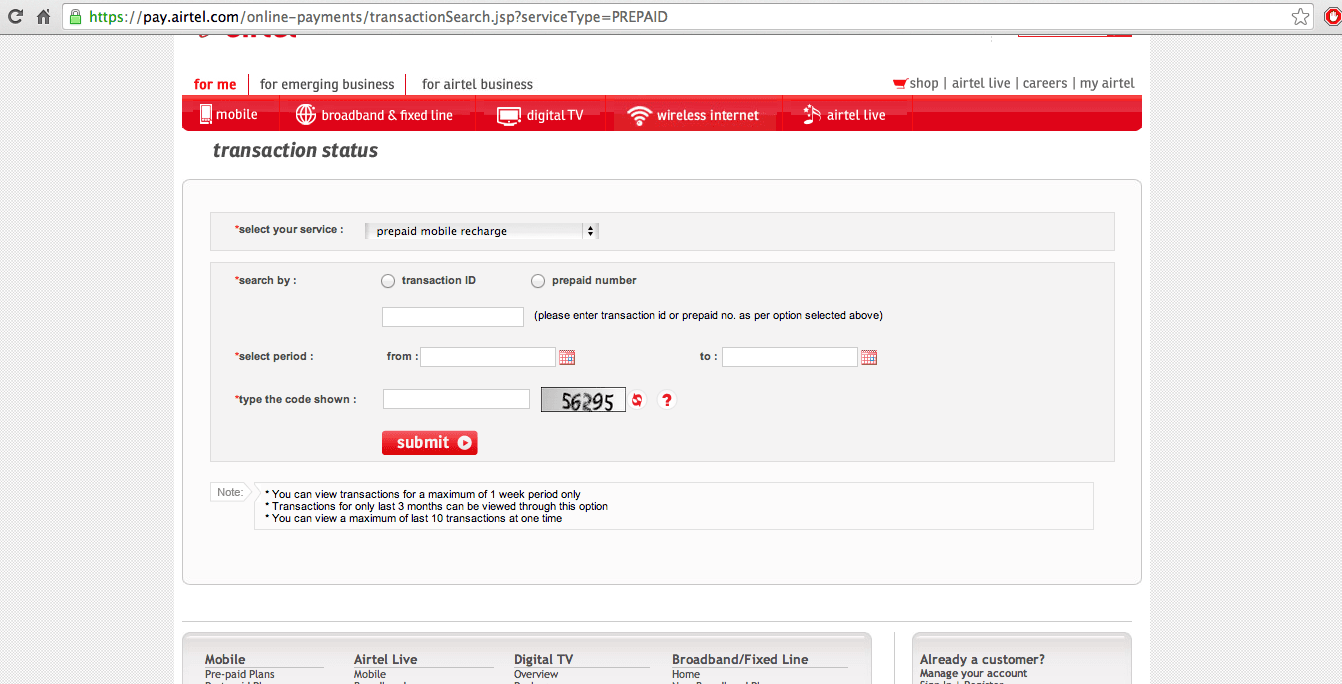
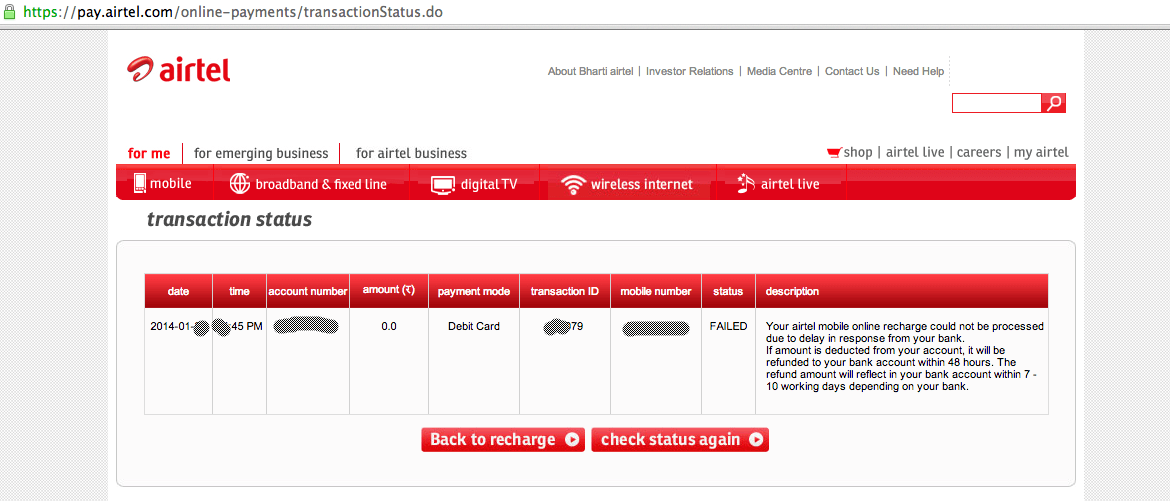
Check any customers transaction details/mobile number
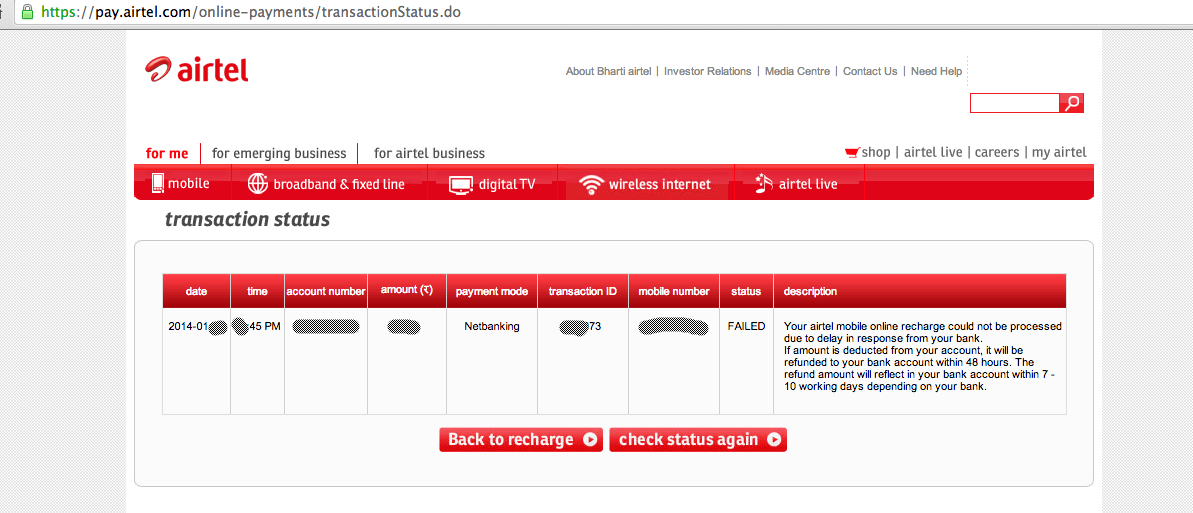
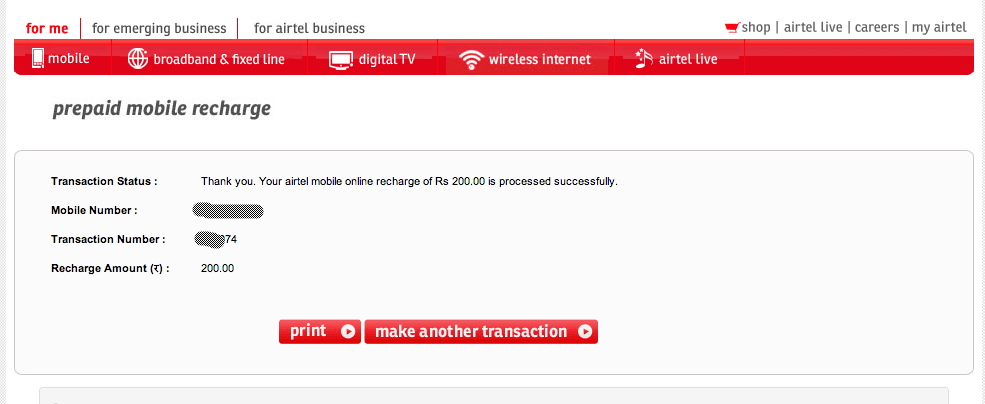
Airtel’s prepaid recharge website also provides the facility to check transaction details for a week’s period. The site just requires a transaction ID or a prepaid number for checking the details. Making things worse is the absence of any second factor of authentication like OTP. Once a user completes a transaction a transaction ID would be generated. Given the fact these transaction IDs were sequential i.e., the next user anywhere in India would receive the next number as the transaction ID (check the numbers in screenshots), anyone could obtain sufficient information about a user including mobile number, recharge values and hence his/her usage pattern. Even the mode of payment used is displayed.
First transaction (somewhere in India)
Our Transaction
Somewhere in India
A bit of social engineering like search for the mobile number in Truecaller like website will provide the name and location of the user. This search can further be extended to other social networks to obtain further information.
We had written about this issue to Airtel few days ago, and it appears that they have fixed it now. Readers must note that this issue was open since months, and we can't think of how many mobile numbers have fallen into wrong hands? Who is to be blamed for this - Airtel or the company who designed the website? Now transaction search requires mobile number, and Airtel sends an OTP to proceed further.
So your data is safe in terms of transactions but the first issue of handset model being displayed is still on. This design flaw from Airtel has disclosed customer information, usage pattern, mode of payment of categories like Postpaid, fixed line/broadband, digital TV subscribers.
Have you ever received random OTA Settings from Airtel or any other operator?
Update 26 Jan 2014, 11:15 hrs IST
We received an update from Airtel regarding this today:
"At Bharti Airtel, customer satisfaction & feedback has always been of utmost importance. We take these feedback very seriously which has helped us deliver services that are world-class, innovative and affordable making us one of best services brand in the country. We welcome such valuable feedback that helps making our systems and processes more robust.”
- airtel spokesperson















