Everything is going Digital – including the Money! In fact, it already is. We pay and exchange goods and services with that imaginary and unfelt digital currency. If something goes wrong, the hard earned money just vanishes in a fraction of a second with the same ease as one uses it digitally. At this juncture, as a TelecomTalk’s initiative, we felt there is a need to emphasize the importance of mobile/data security in our daily lives and bring awareness to our readers. In fact to be real and rude, while being an essential commodity, mobile not only has become a part of life but also has become an addiction too for some users.
As only the mobile device will be in the scope of a user, let us focus only on the consumer aspect (mobile device) now as the security at the rest of the crucial points will be taken care by the respective service providers.

Possible areas of Vulnerability:
1. Mobile Device
2. Connectivity – Bluetooth, WiFi etc.
3. WiFi device
4. Cloud Service
5. Teleco Service Provider
6. App Store
7. Website etc.
How can an attacker benefit from attacks?
1. Surveillance – Monitoring your mobile phone activities.
2. Finance – Steal your financial information stored on the device.
3. Data Theft – Steal any of your valuable data and use it for further attacks.
4. Bot-net – Your device will be compromised after the infection and will be in the control of the attacker. This also helps the attacker to use your device and perform other attacks in disguise.
5. Impersonation – Use your identity and pretend to be you for the purpose of entertainment or fraud.
Now, let us look at securing our mobile devices with basic measures and Do’s to be followed in our regular usage. With just a few minutes of initial setup and configuration, one can rest assured of the mobile and data security.
Possible measures to be followed:
1. “Awareness is the Key” – Yes, the first and the foremost measure is nothing more than becoming aware. It’s ok to spend some time initially and get to know the things. Be completely aware of what you are doing with your mobile. Your ignorance is the key to attackers intrusion into your device.
2. Physical Access: Do not leave your phone unattended and unlocked. Never give your phone to anyone untrustable and ignore, keep an eye on their activities. Any wrong intended person may install an app which includes services [These are the processes which have the highest access and privileges to your phone to perform your regular device tasks] to run in the background and steal/hog your data. Some malicious apps after installation don’t even show up in your app list. They just hide and do the task for the attacker by stealing your data.
3. *SIM Level: Proceed to this step only if you are confident, else skip. Enable SIM PIN in the security settings of your phone. * Check with your operator on service availability and for support.
Enabling this feature can help curb the availability of any contacts/SMS stored on your SIM to strangers in case of theft/lost the device. You can stop the generation of OTP and prevent any account reset related activities before your SIM services get blocked by your service provider.
4. Software Updates: Always install software updates and patches if any. Do not ignore them.
a) OS: Enable Auto Software Update check and Notify if available. Always update to the latest OS version and patches if any provided by your device/os vendor. These updates may contain any security fixes and help protect against any possible vulnerabilities. Make sure your device is on the latest OS version as provided by your vendor.
b) Apps: If the apps installed on your device are vulnerable, then your security is also at stake. Attackers can target certain applications or their servers and steal the data too. So, make sure you update your apps regularly and get the maximum of security.
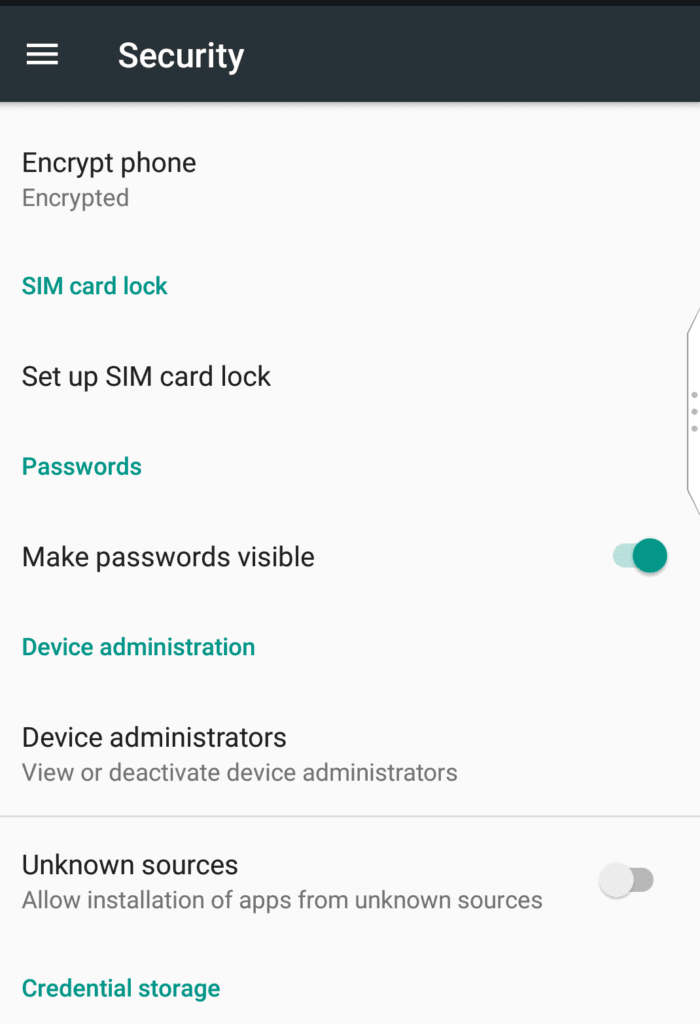
5. Security options inbuilt the device:
Enable basic security features inbuilt the device as per your convenience:
a) Enable device restart password, Automatic screen/device lock or screen/device wake-up lock.
b) Enable device/screen lock with the shortest time possible.
c) Enable Storage and Media Card Encryption.
d) Consider setting up a Lock Screen Message.
e) Enable Auto Wipe/format option after repeated wrong password attempts. *Enable at your own preference if in case kids access your device.
6. Enable Security Measures provided by OS vendor if not enabled by default:
a) Enable Remote Wipe feature in the settings of your OS vendor portal.
b) Enable Find my Device/ Locate your device / Find my iPhone feature.
7. Connectivity:
a) Never connect to open WiFi hotspots or Bluetooth devices. Open wifi networks/ Bluetooth connections allow attackers to intercept data transmission. They can sniff the packets and may steal your sensitive data. They can also do session hijacking by intruding in the network.
b) Never leave Bluetooth/WiFi switched on for longer times in detectable mode. Attackers in the idle time may try various intrusion ways to compromise your device and bring it down.
8. Custom ROMS/OS/Jail Break/Rooting:
Do not install custom OS/ROMS on your device. Doing so, not only voids your device warranty but also makes your device more vulnerable to attacks. Chances are also high that the custom OS might contain malware and is completely undetectable by any antivirus solution. You will lose any *sandbox privilege built by the hardware/OS vendor by default and any app that runs on the phone, will run with full privileges. This is more dangerous as you will be in the complete control of the malware if incase exists on the custom ROM. If in case you are an enthusiastic tinkerer, make sure of the sensitive information you handle via the phone and save on your device.
9. App Store / 3rd Party Applications from Unknown Sources:
The gateway to all the hurdles and intrusions and the main culprit; Disable Application Installations from unknown Sources and a majority of your risk is mitigated.

9. App Store / 3rd Party Applications from Unknown Sources:
a) A security setting that is the main culprit and a gateway to all the hurdles and intrusions. Disable Application Installations from unknown sources and there you go, a majority of your risk is mitigated.
b) Do not install Apps with even popular app titles out of the store. These apps may come bound with undetectable malware and steal your data, corrupt your data or even install aware.
c) Do not even install applications from your friends for testing purposes before they go live on respective stores unless you completely trust them. They may even install active services which monitor your mobile usage and steal data.
10. General measures:
a) Do not browse untrusted and insecure websites or share your personal information on such sites.
b) Do not download anything from unknown or untrusted sites and run it by giving permissions. Always have an eye on the URL in the browser and the URLs behind any links.
c) Do not open any million $ lottery links forwarded via SMS or emails. They are just spam and may lead to something else. Also, do not open any shortened URLs from unknown sources.
d) In a recent news, attackers even bypassed Google play store security and published apps which contained malware. So, awareness is the only key measure which helps you the most.
e) Always have a diligent view of happenings in your mobile. Monitor any excess data usage/activity in the background. There may be an app hogging your data to its servers in the background for which you may blame your operator for charging excess data usage.
f) Attackers are nowadays exploiting vulnerabilities in various applications and executing tasks based on their requirements. There are other ways of exploits too which are out of the scope of an end user and for this story.
g) Hardware related vulnerabilities and exploits are not considered and are out of the scope of this story. Network: interception of data over the air, Hardware: Baseband layer attacks, Mobile Interceptors which hijacks conversations and SMS, jammers are examples of some external hardware related attacks. Only measures which are in the scope of an end user without any external tools – hardware or software are discussed here.
h) Always encrypt your storage. Check carefully the authorization and authentication requests.
i) Always update your WiFi router/Dongle/Wingle’s firmware to the latest available.
j) Always use data access point (APN) provided by your service provider.
Reporting – Report an Incident:
Be responsible and report any incident you come across if it is in the scope of your understanding. It may help the entire community and companies to release a possible fix as soon as possible. Keep required contacts handy, and report immediately the possible loss of your device/credit cards so that any possible damage can be controlled. You can also be legally/financially safe if you complain any of such incidents or theft/loss of payment cards in case of any lost card liability issues.
Prevention is always better than cure.
Security Series Level: TelecomTalk Basic Consumer Awareness L1
In our opinion, if you are aware of the things you are performing and whats running on your mobile, you don’t even need an antivirus solution. Some steps may be time-consuming and pain taking for following, but it is you who decides on your data/device protection before something goes wrong terribly.
Dear Readers, by following the above measures you can be sure that your devices are secure from your end except for any zero-day vulnerabilities or exploits happening at rest of the areas in the mobile device ecosystem. Do you have any questions or suggestions? You can tweet me at @Srikapardhi or comment your opinions on the story or share your experiences below.
Disclaimer: Usage of an antivirus solution is at the discretion of a mobile user. Language terminology may be tweaked or deviated from the Information Security perspective for the understanding of a novice user. Any exploit happened at any third party/vendor is out of the scope of this story. Only Android and iOS device platforms are considered. Enable settings/configuration discussed above at your own interest and discretion. Please google to understand any technical terminology used for more understanding.
If this article saved you time or helped you decide better, consider supporting our work.